While blockchain technology has attracted a broad interest over the last few years, it remains an obscure and elusive concept for consumers and policy-makers. Blockchain technology facilitates the secure exchange of value between individual and/or entities within trading platforms, allowing for a secured maintenance of records. The application of blockchain can benefit both public and private entities across sectors, on the condition that they address the inherent challenges of blockchain and create a regulatory framework for its uptake.
Defining Blockchain and its Features
Blockchain is a type of Distributed Ledger Technology (DLT) consisting of a decentralized network of immutable databases shared among those within the network, where no single participant has independent or exclusive control over data.
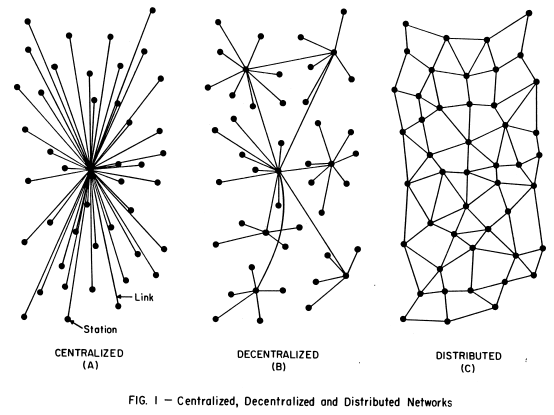
Its decentralised nature reinforces network security. In traditional networks, the entire system relied upon the points in the centre — central management node. If these points were weakened or failed completely, the effectiveness and integrity of the entire system could be compromised. By eliminating the need for a central management node, blockchain ensures that information is preserved even if individual nodes are removed (See Figure 1). Additionally, blockchain can reduce the transactional cost of performance paid to the intermediary and minimise the risk of collusion.
Source: Paul Baran, On Distributed Communications Networks
Blockchain is built on three established technologies. First, building on traditional ledgers, blockchain uses distributed ledgers – a network of databases maintained and revised independently by each participant (or node). Second, timestamping provides an additional layer of security by displaying an exact record for data entries (including time, date and modification history). Finally, much like written signatures, digital signatures are used to confirm identity and prove that a message or information has originated from a specific person. Digital signatures, along with hash functions – the mechanism used by What’s App for its end-to-end encryption feature – provide a secure method of digital data transmission. The combination of digital signatures and timestamping removes the need for an intermediary to check the authenticity of various types of transactions.
There are two main types of blockchain: public and private. In public networks, there is no centralised management function, access can be granted without permission and the network can be joined anonymously. Consequently, anyone can view the data contained within the network and participate in the consensus process. Within private networks, permission to access must be given by the network creator or existing participants to obtain the rights to view certain data and participate in the consensus process. Otherwise, rights to do so are restricted to nodes in the network.
Blockchain in Action
When a digital transaction is carried out, it is grouped with other transactions sent out to the entire network in a cryptographically-protected block using hash functions. Certain members (known as ‘miners’) in the network with high levels of computing power then compete to validate the transactions by solving complex coded problems, known as the consensus process. For example, miners within the Bitcoin blockchain network taken part a similar process called Proof-of-work with the first miner to solve the problems and validate the block receiving Bitcoins as a reward.
The validated block of transactions is then timestamped and added to a chain in a linear, chronological order of new blocks of validated transactions. These are linked to older blocks, resulting in a chain of blocks and creating a ledger with the blockchain’s transactional history. The entire network is continually updated to ensure uniformity across all the ledgers in the network and each member of the network is provided with the information to determine ownership of the assets of any other member at any given time.
Challenges Encountered by Blockchain
One challenge associated with blockchain technologies relates to immutability since transactional data can only be added to the network but cannot be modified nor removed, raising concerns for some businesses if false data is added. In addition, there is a risk of infringing the GDPR’s ‘right to be forgotten’ when storing personal data in a blockchain which cannot be erased if a user wishes to leave the network. A solution to this was developed by Lition, a blockchain company based in Germany which stores provide data off-chain — outside the blockchain network — where it can be removed when required.
Another consideration relates to the scalability of blockchain and the concept of interoperability. Currently, all blockchain networks have their own ecosystem (consensus mechanism and community of users) and operate in their respective silos, preventing the transfer of information or value across siloed blockchains and limited the size of networks.
The decentralised nature of the blockchain also presents issues with regards to liability within the blockchain. For example, this raises concerns regarding accountability in case of fraud, creating legal and ethical grey areas.
Finally, the environmental cost of some public blockchains presents a challenge. For some public blockchains, the consensus process uses a high amount of energy. For example, Bitcoin’s mining network uses more electricity in a year than the whole of Ireland. Fortunately, Algorand developed an environmental-friendly blockchain network, achieving a consensus through the Proof of Stake mechanism (consensus process) which consumes far less electricity than the Bitcoin network.
As the adoption of blockchain technology continues to increase across sectors, industry actors will rely on standards and a regulatory framework to ensure its secure application. Additionally, collaboration between the private and public sector is critical to tackle any misperceptions regarding the technology and build consumer trust.
Author: Srimukessh Subramanian, Consultant, Technical Policy and Regulatory Environment, Access Partnership
Read part 2: Blockchain: A Regulatory Overview